An organization has spent six months building
a DPDPA compliance framework. The consent mechanism is solid. Privacy notices
are itemized. Internal data handling policies are documented.
Then a third-party analytics vendor onboarded three years
ago suffers a breach — and 2 million customers' personal data is exposed.
Under DPDPA 2023, that's the organization's problem.
Not the vendor's. The organization's. Because under Indian
data protection law, the Data Fiduciary bears the obligation to ensure
that every Data Processor acting on its behalf processes personal data only in
accordance with instructions, for the specified purpose, and with adequate
security safeguards.
This is the compliance blind spot most Indian businesses
haven't addressed. And it might be the most expensive one.
Why Third-Party Risk Is the Biggest DPDPA Gap Right Now
Most DPDPA readiness efforts are focused inward — internal
data mapping, consent mechanisms, privacy policies. That's necessary but
insufficient.
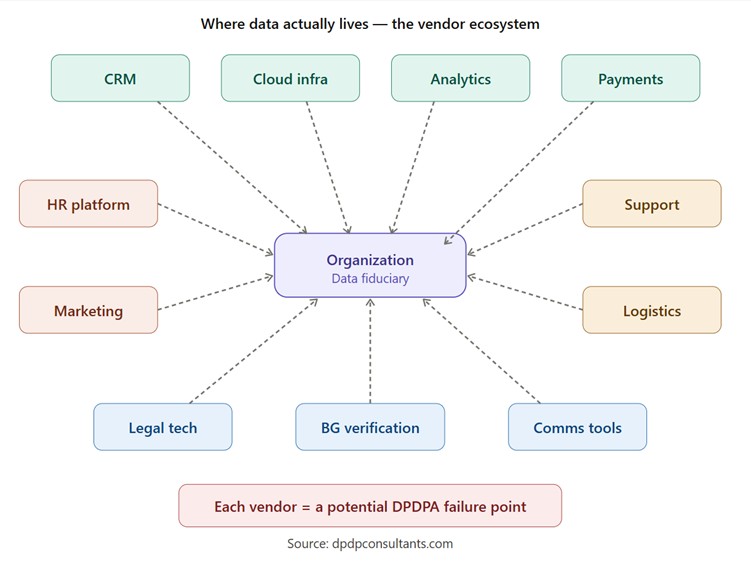
Consider the average mid-to-large Indian enterprise's data
ecosystem:
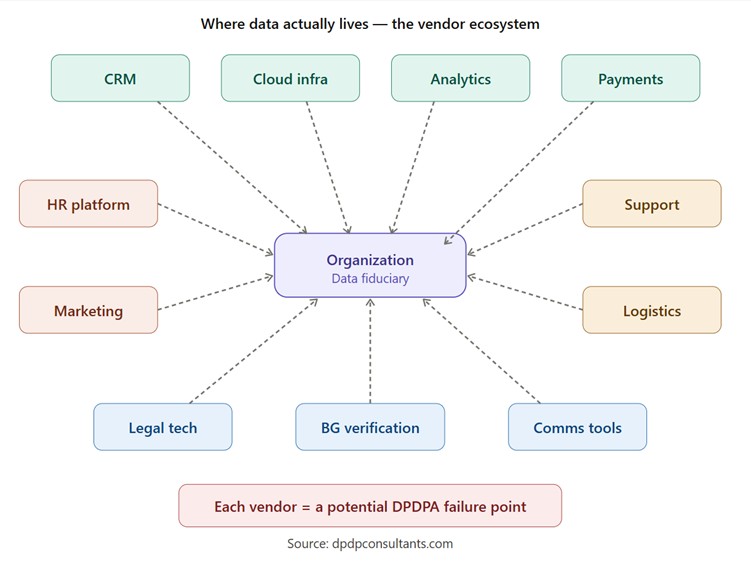
A typical enterprise shares personal data with 20 to 50+
third-party vendors. Each one is a potential failure point under DPDPA. And
most organizations have:
- No
standardized assessment of vendor data handling practices
- No
DPDPA-specific clauses in existing vendor contracts
- No
ongoing monitoring of whether vendors are processing data within scope
- No
incident response protocol that includes vendor-triggered breaches
This isn't a theoretical risk. It's the most likely way an
organization will face DPDPA enforcement action.
What DPDPA Says About Data Processors (and Why It's Stricter Than Most Think)
Let's be precise about the legal framework.
Key Definitions
|
Term
|
DPDPA
Definition
|
What It
Means for Organizations
|
|
Data
Fiduciary
|
Any person
who determines the purpose and means of processing personal data
|
The
organization — it decides why and how data is processed
|
|
Data
Processor
|
Any person
who processes personal data on behalf of a Data Fiduciary
|
The vendors —
they process data because the organization told them to
|
The Critical Legal Position
Under DPDPA 2023, obligations rest primarily on the Data
Fiduciary, not the Data Processor. This is a fundamental architectural
choice in the law. It means:
- The
Fiduciary chooses the processor — so the due diligence obligation
falls on the Fiduciary
- The
Fiduciary defines the purpose — so any processing beyond that purpose
is a governance failure
- The
Fiduciary must ensure security — reasonable security safeguards apply
to data wherever it lives, including vendor systems
- The
Fiduciary reports breaches — if a vendor breach affects Data
Principals' data, the Fiduciary notifies the Data Protection Board
Translation: Organizations can outsource data
processing. They cannot outsource accountability.
The 5 Third-Party Compliance Failures That Will Trigger DPDPA Action
Failure 1: No Vendor Data Inventory
Organizations can't protect what they can't see. Most
businesses cannot answer a basic question: Which vendors have access to which
categories of personal data belonging to which Data Principals?
Without this inventory, it's impossible to:
- Assess
risk by vendor
- Respond
to Data Principal access or erasure requests (the data location is
unknown)
- Scope
the impact of a vendor breach
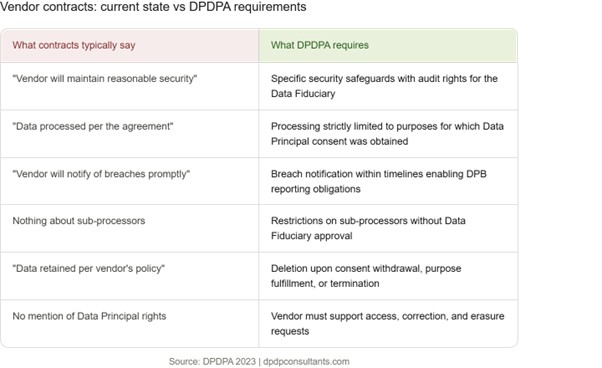
Failure 2: Legacy Contracts Without DPDPA Clauses
Contracts signed before DPDPA was enacted likely don't
include:
- Purpose
limitation aligned with DPDPA's specific consent requirements
- Obligations
to process data only per the Data Fiduciary's instructions
- Breach
notification timelines that allow the Fiduciary to notify the DPB within
the required window
- Data
deletion obligations upon contract termination or consent withdrawal
- Sub-processor
restrictions and approval requirements
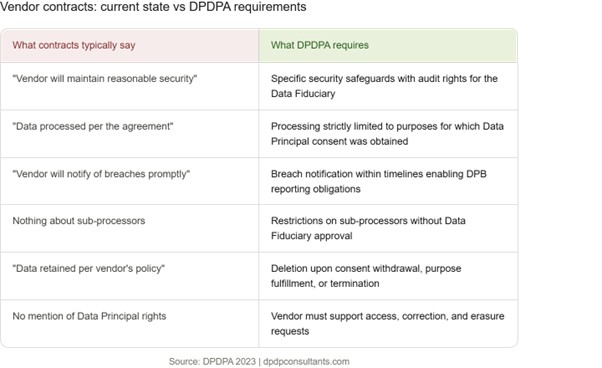
|
What
Current Contracts Likely Say
|
What DPDPA
Requires
|
|
"Vendor
will maintain reasonable security"
|
Specific
security safeguards with audit rights for the Data Fiduciary
|
|
"Data
will be processed per the agreement"
|
Processing
strictly limited to the purposes for which Data Principal consent was
obtained
|
|
"Vendor
will notify of breaches promptly"
|
Breach
notification within timelines that enable the Fiduciary to meet DPB reporting
obligations
|
|
Nothing about
sub-processors
|
Restrictions
on engaging sub-processors without Data Fiduciary approval
|
|
"Data
retained per vendor's policy"
|
Deletion upon
consent withdrawal, purpose fulfillment, or contract termination
|
|
No mention of
Data Principal rights
|
Vendor must
support the Data Fiduciary in fulfilling access, correction, and erasure
requests
|
Failure 3: No Pre-Onboarding Assessment
Under DPDPA, onboarding a vendor that processes personal
data without assessing their data protection posture is a governance failure.
Organizations need to evaluate:
- What
personal data categories the vendor will access
- Where
they store and process it (especially cross-border implications)
- Their
security architecture and breach history
- Their
sub-processor chain
- Their
ability to support Data Principal rights obligations
Failure 4: No Ongoing Monitoring
Assessment at onboarding isn't enough. Vendor risk is
dynamic. The vendor that was compliant last year may have:
- Changed
their infrastructure or sub-processors
- Suffered
a breach they didn't disclose
- Been
acquired by another entity with different data practices
- Expanded
their data processing beyond the original scope
Failure 5: No Incident Response Integration
When a vendor has a breach, the clock starts ticking on the
organization's notification obligation to the Data Protection Board. If the
incident response plan doesn't include:
- Vendor
breach escalation channels
- Pre-agreed
notification timelines in contracts
- A
process to assess which Data Principals are affected
- Coordination
protocols between the internal team and the vendor's
...then the scramble begins when it matters most.
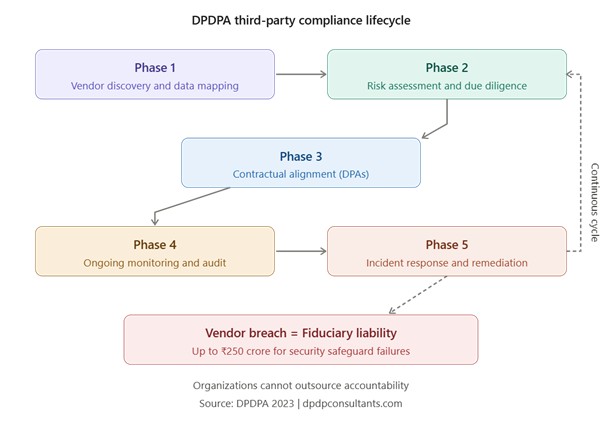
Building a DPDPA Third-Party Compliance Framework
Here's the architecture that actually works:
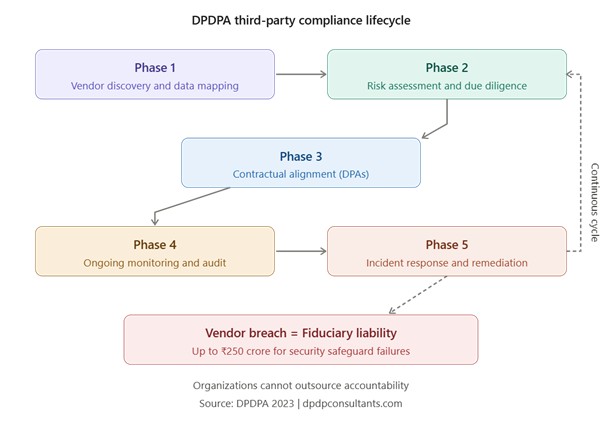
Phase 1: Vendor Discovery & Data Mapping
Build a complete inventory of every vendor, tool, platform,
and service provider that touches personal data. For each, document:
- Data
categories shared
- Processing
purposes
- Data
flow direction (organization → vendor, vendor → sub-processor, etc.)
- Storage
locations
- Access
controls
Phase 2: Risk Assessment & Due Diligence
Not all vendors carry equal risk. A cloud infrastructure
provider hosting the entire database is a different risk profile than a
font-rendering CDN.
Tier vendors by risk:
|
Risk Tier
|
Criteria
|
Assessment
Depth
|
|
Critical
|
Stores/processes
large volumes of sensitive personal data, has direct Data Principal access
|
Full
assessment: security audit, data handling review, breach history,
sub-processor mapping, on-site/virtual assessment
|
|
High
|
Processes
personal data in core workflows (CRM, HR, analytics)
|
Detailed
questionnaire + documentation review + contractual safeguards
|
|
Medium
|
Limited
personal data access, ancillary to core processing
|
Standard
questionnaire + contractual safeguards
|
|
Low
|
No direct
personal data processing, or fully anonymized data only
|
Contractual
acknowledgment + periodic review
|
Phase 3: Contractual Alignment
Every vendor processing personal data needs a Data
Processing Agreement (DPA) that includes DPDPA-specific provisions:
- Processing
limited to specified, consented purposes
- Instructions-only
processing (no autonomous use of data)
- Security
safeguard obligations with audit rights
- Breach
notification within contracted timelines
- Sub-processor
restrictions and approval mechanisms
- Data
deletion upon purpose completion, consent withdrawal, or termination
- Cooperation
on Data Principal rights (access, correction, erasure)
- Indemnification
for compliance failures originating at the vendor
Phase 4: Ongoing Monitoring & Audit
Compliance isn't a one-time check. Organizations should
build a monitoring cadence:
- Quarterly:
Automated compliance status checks for critical vendors
- Semi-annually:
Detailed reassessment for high-risk vendors
- Annually:
Full portfolio review and vendor re-tiering
- Trigger-based:
Immediate reassessment upon vendor breach, acquisition, or significant
change
Phase 5: Incident Response & Remediation
Pre-wire incident response to include vendor scenarios:
- Vendor
breach notification received → immediate impact assessment
- Determine
affected Data Principals and data categories
- Notify
Data Protection Board within required timelines
- Coordinate
with vendor on containment and remediation
- Document
everything for regulatory inquiry
The Cross-Border Dimension: Why This Gets More Complex
Under DPDPA, the Central Government may restrict transfer of
personal data to certain countries. If vendors process data outside India —
which is extremely common with global SaaS tools — organizations need to:
- Map
which vendors transfer data abroad and to which jurisdictions
- Monitor
the government's restricted country notifications
- Ensure
contractual provisions address cross-border transfer requirements
- Have
contingency plans if a vendor's processing jurisdiction gets restricted
This is an evolving area, and most organizations haven't
even started mapping their cross-border data flows through vendors.
The Real Cost of Ignoring Third-Party Risk
Risk
Scenario | DPDPA
Consequence |
Vendor breach
exposing Data Principal data | Data
Fiduciary liable for failure to implement reasonable security safeguards — up
to ₹250 Crore |
Vendor
processing data beyond consented purpose | Invalid
processing — failure to fulfill data fiduciary obligations — up to ₹50
Crore |
Vendor fails
to delete data after consent withdrawal | Non-compliance
with Data Principal rights — up to ₹200 Crore |
Unable to
respond to DPB inquiry because vendor data flows aren't documented | Operational
paralysis + enforcement risk |
Stop Treating Vendors as Someone Else's Problem
Here's the leadership reframe that matters: the vendor
ecosystem IS the compliance perimeter.
Every SaaS tool, every cloud provider, every analytics
platform, every outsourced process that touches personal data extends an
organization's DPDPA obligations. If a business can't assess, contract,
monitor, and respond across that entire perimeter, internal compliance efforts
are incomplete.
This requires more than a spreadsheet and annual vendor
reviews. It requires a systematic third-party assessment framework — one
that is DPDPA-specific, risk-tiered, continuously monitored, and integrated
with consent management and incident response systems.
Vendors are a liability. Make them a strength.
Get a Free Third-Party DPDPA Risk Assessment →
DPDP Consultants' Third-Party Assessment tool maps
the entire vendor data ecosystem, risk-tiers every processor, generates
DPDPA-compliant DPA templates, and provides ongoing monitoring dashboards — so
organizations are never caught off guard by a vendor they forgot to assess.
Pair it with the Consent Manager to ensure vendor
data processing stays aligned with active Data Principal consent, and the Impact
Assessment tool to quantify the risk each vendor introduces.
Booka Consultation →